What Is STIR/SHAKEN? How the Robocall Authentication Framework Works (And What It Means for Your Business)
BA

Chances are you’ve seen “Spam Risk” flash across your phone screen before you even thought about answering. That warning — and the entire system behind it — exists largely because of a framework called STIR/SHAKEN.
If you run a business that makes outbound calls, you need to understand what it is, why it was created, and how it directly affects whether your calls get answered or blocked.
The Robocall Problem That Made STIR/SHAKEN Necessary
Before we get into the framework itself, it helps to understand the scale of the problem it was built to solve.
Robocalls peaked at 58.5 billion calls in 2019 in the United States alone, according to YouMail’s Robocall Index. The core reason so many fraudulent calls got through? The traditional phone network was built on trust, not verification. The caller ID system — developed decades ago — simply displays whatever number the caller claims to be calling from. There was no mechanism to confirm that number was legitimate.
This made caller ID spoofing trivially easy. Scammers could impersonate your bank, the IRS, a local number, or even your own contact list. Consumers became so desensitized that legitimate businesses saw their call answer rates crater — even when calling their own customers.
Regulators and carriers were forced to act.
What Is STIR/SHAKEN?
STIR/SHAKEN is a set of technical standards designed to authenticate caller ID information across the phone network. The name is actually two acronyms stacked together:
- STIR — Secure Telephone Identity Revisited
- SHAKEN — Signature-based Handling of Asserted information using toKENs
Together, they create a system where calls are cryptographically signed by the originating carrier and that signature is verified by the receiving carrier — before the call ever reaches your phone.
Think of it like an email with a digital signature. Anyone can send an email claiming to be from your CEO, but if there’s no valid cryptographic signature from the right domain, modern email security flags it. STIR/SHAKEN does the same thing for phone calls.
How STIR/SHAKEN Works: Step by Step
Here’s what happens in the fractions of a second between when someone dials a number and when your phone rings:
1. The call originates
A caller dials a number. Their carrier — the originating service provider — checks whether that caller is authorized to use the number they’re calling from.
2. The carrier signs the call
If the carrier can verify the caller has the right to use that number, it attaches a digital certificate (called a PASSporT — Personal Assertion Token) to the call using a private cryptographic key. This happens in the SIP (Session Initiation Protocol) signaling layer of modern VoIP networks.
3. An attestation level is assigned
This is critical. The originating carrier assigns one of three attestation levels:
| Attestation | Code | What It Means |
|---|---|---|
| Full Attestation | A | The carrier knows the customer and has confirmed they’re authorized to use this exact number |
| Partial Attestation | B | The carrier knows the customer but cannot confirm the specific number |
| Gateway Attestation | C | The call entered the network from an external gateway; the carrier can’t vouch for it |
4. The signature travels with the call
The signed token is embedded in the call’s SIP headers as it routes across the network.
5. The receiving carrier verifies
When the call reaches the terminating carrier (the one serving the person being called), it checks the digital signature against the originating carrier’s public key via a verified certificate authority. If the signature is valid, the call passes. If it’s been tampered with or is missing entirely, the carrier knows something is off.
6. Your phone displays the result
Depending on the carrier and device, a verified call might show a checkmark, a “Caller Verified” label, or simply pass through normally. An unverified or suspicious call may be flagged as “Spam Risk,” sent to voicemail automatically, or blocked entirely.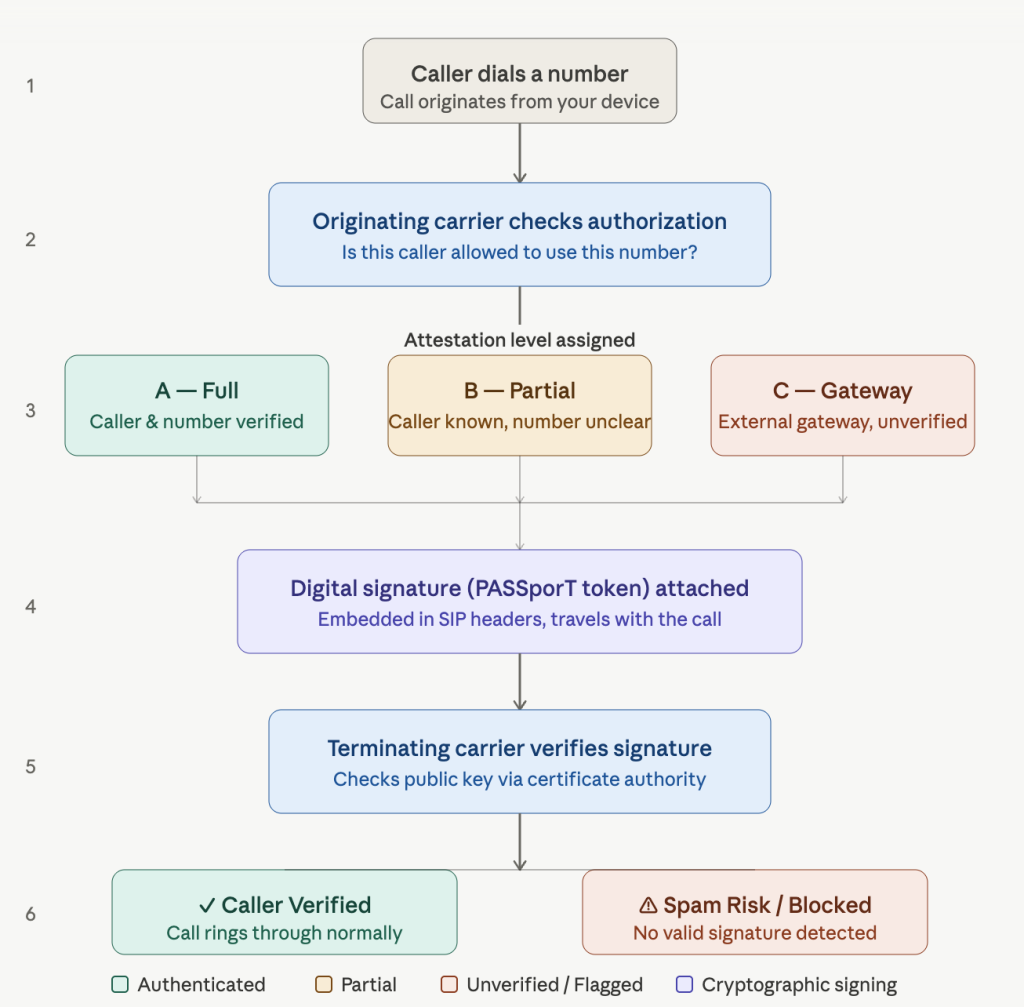
Who Is Required to Implement STIR/SHAKEN?
In the United States, the FCC mandated STIR/SHAKEN implementation through the TRACED Act (Telephone Robocall Abuse Criminal Enforcement and Deterrence Act), signed into law in December 2019.
Key compliance milestones:
- June 30, 2021 — Large voice service providers (over 100,000 subscriber lines) were required to fully implement STIR/SHAKEN in their IP networks
- June 30, 2022 — Smaller providers faced the same requirement, with some exceptions for carriers that had obtained an extension
- Ongoing — The FCC has continued tightening rules, requiring providers that haven’t fully implemented STIR/SHAKEN to file mitigation plans and take other anti-spoofing measures
Canada has implemented similar requirements through the CRTC (Canadian Radio-television and Telecommunications Commission), and other countries are developing their own analogous frameworks.
What Attestation Level Does Your Business Get?
This is where STIR/SHAKEN gets very practical for businesses making outbound calls.
Full Attestation (A) is the gold standard. To receive it, your voice carrier must:
- Know who you are as a customer
- Have confirmed you’re authorized to use the specific calling number on the call
If you’re using a VoIP business phone system and your provider has properly provisioned your numbers, you should generally receive A-level attestation. This means your calls are most likely to pass through carrier filters and display cleanly on the recipient’s screen.
Partial Attestation (B) often applies when your carrier knows you but can’t directly verify the specific number — for example, if you’re using a large block of numbers or calling through a system the carrier has less visibility into.
Gateway Attestation (C) is the lowest level, often applied to calls coming through international gateways or aggregators with less oversight. Calls with C-level attestation are at the highest risk of being flagged or blocked by downstream carriers.
For businesses, the practical implication is this: where you get your phone service and how you’ve set up your calling infrastructure directly determines how your calls are treated by recipients’ carriers.
How STIR/SHAKEN Impacts Robocalling
For illegitimate robocallers, STIR/SHAKEN has meaningfully raised the barrier to spoofing. A scammer claiming to be calling from your bank now has to contend with the fact that the bank’s carrier never signed that call — and the receiving carrier knows it.
That said, STIR/SHAKEN is not a silver bullet. Here’s an honest picture of what it does and doesn’t do:
What STIR/SHAKEN effectively prevents:
- Spoofing numbers from carriers whose signing is verified (a bad actor can’t convincingly impersonate a number they don’t control)
- Unauthenticated calls slipping through as if they were verified
- Consumer confusion about whether caller ID information has been authenticated
What STIR/SHAKEN doesn’t fully solve:
- Calls that originate legitimately but are used for fraud (if a scammer legitimately registers a number, they can get A-level attestation)
- Calls that transit older TDM (non-IP) portions of the network, where the signature can break
- International calls, where implementation varies significantly by country
- Spam or misleading calls from numbers that are technically “authenticated”
This is why STIR/SHAKEN is one layer in a broader anti-robocall strategy — not the entire solution. Carriers also use call analytics, AI-based spam detection, and industry-wide databases like the FCC’s Robocall Mitigation Database in conjunction with STIR/SHAKEN.
What STIR/SHAKEN Means for Legitimate Businesses
Here’s the part most guides skip over: STIR/SHAKEN affects legitimate businesses just as much as scammers — just in different ways.
If your business makes outbound calls — for sales, appointment reminders, customer service, collections, or any other reason — your call answer rates are directly tied to how your calls are authenticated and whether your numbers have accumulated a bad reputation.
Common problems legitimate businesses face:
Numbers being flagged incorrectly
Even with A-level attestation, high call volumes from a single number can trigger carrier analytics to flag your number as potential spam. This happens to call centers and sales teams regularly.
Using a provider that delivers low attestation
Some cheaper VoIP providers or call center platforms route calls through infrastructure that results in B or C-level attestation — meaning your calls look less trustworthy before the recipient even knows who’s calling.
Number reputation damage
Attestation tells carriers the call is authenticated. It doesn’t tell them the number has a good reputation. If your number has been associated with complaints, it can still be flagged even with full attestation.
How to protect your business calling:
1. Use a reputable VoIP provider that implements STIR/SHAKEN properly and can confirm what attestation level your outbound calls receive
2. Register your numbers with the FCC’s Do Not Originate list where appropriate and maintain them with your carrier
3. Monitor your number reputation using tools like Google’s Verified Calls, Free Caller Registry, or carrier-specific lookup tools
4. Diversify your calling numbers rather than hammering a single number with high volume
5. Comply with TCPA and call consent rules — attestation solves authentication, but regulatory compliance is a separate and equally important layer
STIR/SHAKEN and VoIP: Why Your Provider Matters
Traditional landline calls were always somewhat traceable back to a physical address. VoIP changed that — it made it easy to spin up thousands of numbers cheaply and call at scale. That’s exactly what robocallers exploited.
STIR/SHAKEN was built specifically for IP-based calling (SIP networks). When you choose a VoIP business phone provider, one of the questions worth asking is: does this provider fully implement STIR/SHAKEN, and what attestation level do my outbound calls receive?
A provider that has a proper relationship with carriers, maintains clean number inventories, and participates in the STIR/SHAKEN ecosystem will give your business calls the best chance of reaching the people you’re trying to reach — verified, unflagged, and answered.
The Future of Call Authentication
STIR/SHAKEN is evolving. The FCC and industry groups continue to expand its reach and close gaps:
- International STIR/SHAKEN frameworks are being developed through organizations like ATIS and ITU to extend authentication to cross-border calls
- Analytics layering is becoming more sophisticated — carriers are combining cryptographic attestation with behavioral data to catch authenticated-but-abusive callers
- Branded calling initiatives like CNAM (Caller Name) upgrades and branded caller ID (showing a logo alongside a verified name) are emerging as the next layer on top of authentication
- FCC enforcement is escalating, with carriers now able to block calls from non-compliant providers at the network level
The trend is clear: the phone network is moving toward a world where every call has an authenticated identity, and calls without one face increasing friction.
Key Takeaways
- STIR/SHAKEN is a call authentication framework that cryptographically verifies caller ID information using digital certificates
- It was mandated in the US by the TRACED Act and is now required for virtually all voice service providers
- Calls receive an attestation level (A, B, or C) indicating how confidently the originating carrier can vouch for the caller’s identity
- For businesses, this means your choice of phone provider and how your numbers are set up directly affects whether your calls get answered or flagged as spam
- STIR/SHAKEN reduces spoofing but doesn’t eliminate all robocall threats — it’s one layer in a multi-layered defense
- Legitimate businesses should actively manage their number reputation, use compliant providers, and stay current with FCC rules
RingQ provides business VoIP solutions built on compliant, carrier-grade infrastructure — so your calls get through to the people you’re trying to reach. Learn more about how RingQ handles call authentication and number reputation for your business.
If you have more questions about the STIR/SHAKEN method, get in touch with our team.
See Also



